A researcher has discovered seven critical security vulnerabilities with Thunderbolt that impact Windows, Linux and, to a lesser extent, macOS.
In late April it was reported that one of Microsoft’s reasons for not including Thunderbolt on its Surface devices was concerns over security. Specifically, Microsoft had concerns that, because Thunderbolt acts as a direct memory access port, a hacker could use a memory stick or other peripheral to gain direct access to the device’s memory.
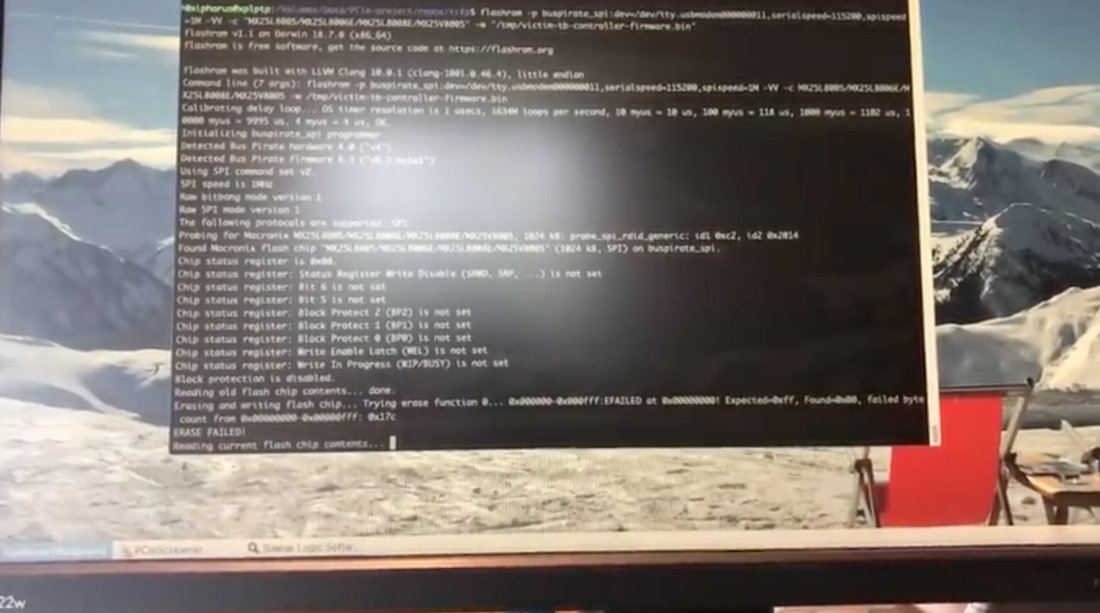
It seems Microsoft’s concerns may not have been so far-fetched after all. Björn Ruytenberg, researcher at Eindhoven University of Technology, has published a report detailing seven Thunderbolt vulnerabilities that could allow a hacker to theoretically steal all data on a computer, regardless of what security measures are in place, such as password protection or encryption. In a video demonstrating the vulnerabilities, Ruytenberg gains access in roughly five minutes.
Of the vulnerabilities, all seven impact both Windows and Linux, while only two impact macOS. Even then, macOS is only partially affected, as Apple’s computers use two security measures not used by Windows or Linux. The vulnerability compromises the first measure, but not the second. If running Windows or Linux in Boot Camp, however, a Mac becomes “trivially affected.”
In a follow-up blog, Ruytenberg says Intel was notified in mid-February, but has no intention of taking any further action, citing action they have already taken. In a blog post on the company’s site, Intel’s Jerry Bryant explained the mitigation efforts already in place:
“In 2019, major operating systems implemented Kernel Direct Memory Access (DMA) protection to mitigate against attacks such as these. This includes Windows (Windows 10 1803 RS4 and later), Linux (kernel 5.x and later), and MacOS (MacOS 10.12.4 and later). The researchers did not demonstrate successful DMA attacks against systems with these mitigations enabled. Please check with your system manufacturer to determine if your system has these mitigations incorporated. For all systems, we recommend following standard security practices, including the use of only trusted peripherals and preventing unauthorized physical access to computers.”
While a vulnerability of this kind is disconcerting, it’s important to keep it in perspective. The vulnerability requires physical access to a machine. As we wrote in the article describing Microsoft’s decision not to include Thunderbolt, “a long-standing rule of computer security is that once physical access has been achieved, all bets are off.“ That rule still holds true.
In the meantime, if Intel’s response is accurate, it seems modern computers with the latest OS updates are largely safe. In the meantime, common sense measures, such as controlling computer access and not plugging in unknown Thunderbolt devices, should go a long way toward protecting all users.






 WebProNews is an iEntry Publication
WebProNews is an iEntry Publication